94% of Long-Running Bug Bounty Programs On Immunefi Have Surfaced a Critical Vulnerability
Every protocol team believes the same thing: “We’ve been audited. Our code is solid. A critical vulnerability? That’s something that happens to other teams.”
Five years of data from Immunefi says otherwise. And when you pair it with what we know about the real cost of getting hacked, the case for continuous security coverage becomes mathematically clear.
We analyzed confirmed and paid vulnerability reports across 593 bug bounty programs on the Immunefi platform, spanning January 2021 through February 2026. We excluded audit competitions and attackathons to focus on ongoing, persistent bug bounty programs, the kind that run month after month, year after year, providing continuous security coverage.
The findings are unambiguous.
Confirmed Criticals Are Only a Matter of Time
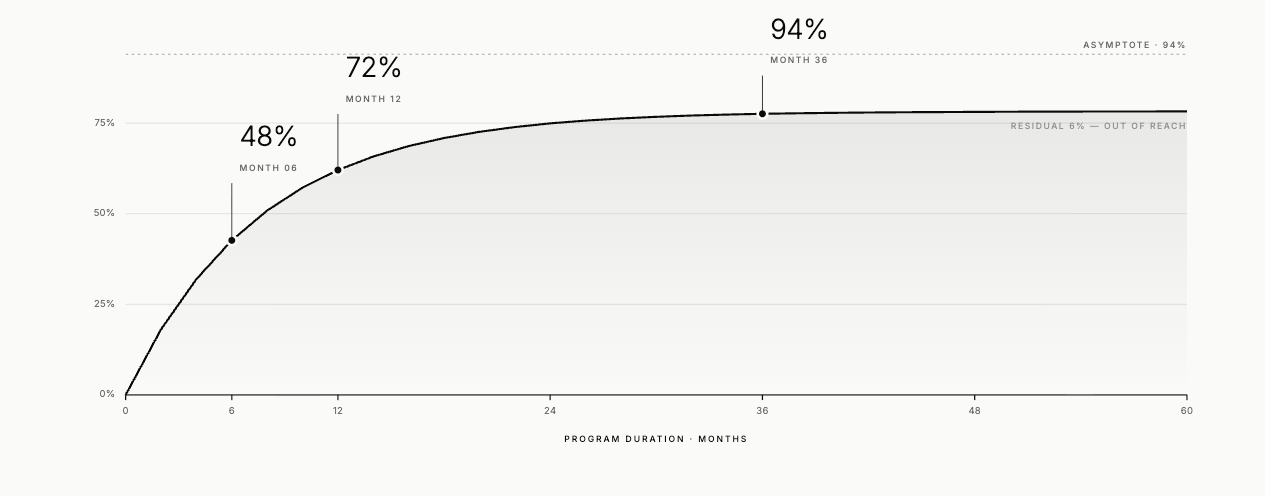
Among bug bounty programs that have been active for five or more years on Immunefi, 93.9% have received at least one confirmed, paid critical severity vulnerability report. Not a theoretical risk. Not an informational finding. A confirmed critical, the kind of vulnerability that means drained funds or total protocol compromise.
The trend is monotonic and unmistakable. The longer a program runs, the closer the critical discovery rate climbs toward 100%:
1+ years active: 61.4% of programs have surfaced a critical
2+ years: 73.9%
3+ years: 87.2%
4+ years: 92.9%
5+ years: 93.9%
These are not programs that launched bounties because they suspected problems. This is the natural outcome of exposing complex, high-value code to sustained adversarial review. Critical vulnerabilities are an inherent property of software at this level of complexity, and if you invite the global security community to find them, eventually they will.
A Persistent, Recurring Pattern
One finding that surprised us: critical vulnerabilities are not a one-time discovery. Among the 364 programs that have surfaced at least one critical, the average is 2.7 confirmed criticals per program, with a median of 2. One program has received 50 confirmed critical reports over its lifetime.
More tellingly, 129 programs, over a third of those with criticals, have had critical severity bugs surface in two or more separate calendar years. When new code gets shipped, new attack surfaces emerge, and new vulnerabilities are inevitably created with them.
This pattern maps directly to what we documented in The Real Cost of an Onchain Hack: 2024-2025 Update. There, we tracked 425 hacks across five years and found that the overall count of exploits has not declined. It has settled into a steady, elevated baseline of roughly 95 incidents per year. The bugs keep appearing because the code keeps changing. The question is whether they get found by a researcher or by an attacker.
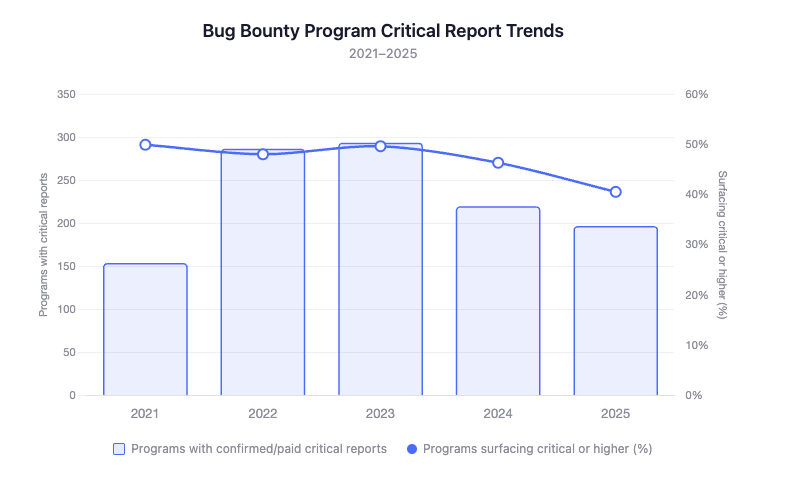
The Annual Critical Disclosure Rate Is Stable
Roughly half of all active bug bounty programs on Immunefi surface at least one critical vulnerability in any given year. This has held steady across five full calendar years, through bull markets and bear markets, and across wildly different protocol architectures:
This consistency is meaningful: It means the critical vulnerability rate isn’t driven by a handful of poorly written protocols dragging up the average. It’s a structural feature of every blockchain software project when skilled researchers examine it continuously. It’s how crypto is, and will continue to be.
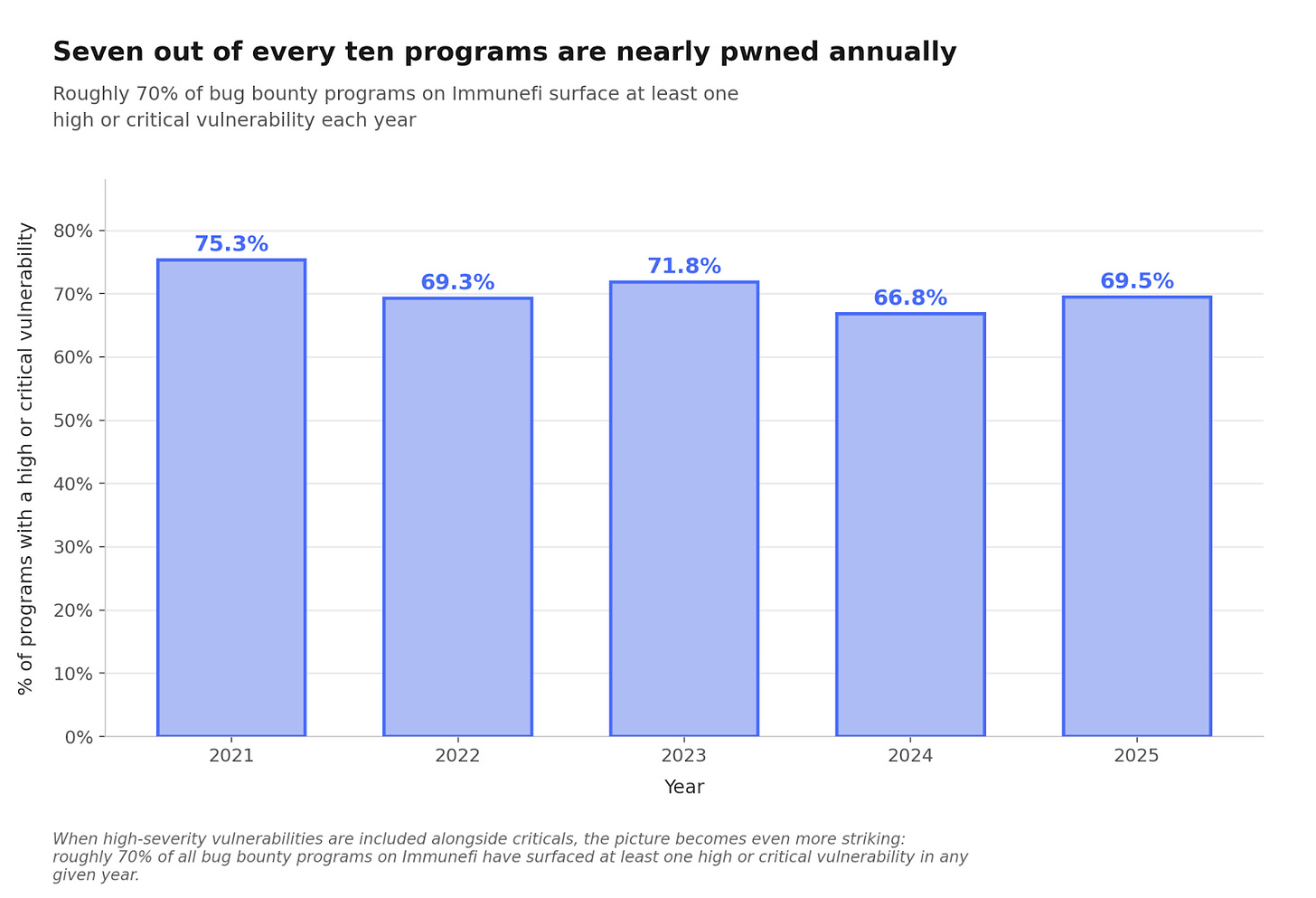
Expand to High Severity and It’s Nearly Universal
When we include high severity vulnerabilities alongside criticals, the numbers become even more striking: roughly 70% of all bug bounty programs on Immunefi have surfaced at least one high or critical vulnerability in any given year. Seven out of every ten programs are nearly pwned annually.
The remaining 30% are predominantly newer programs that simply haven’t had enough time or researcher attention yet. Given the trajectory the data shows, they will all get highs/criticals eventually.
$20,000 vs. $25,000,000: The Economics of Finding It First
This is where the vulnerability discovery data and the hack impact data converge into a single, unavoidable conclusion.
Across our dataset, Immunefi bug bounty programs have paid out $107.3 million just for confirmed critical vulnerabilities. The median payout for a bug bounty critical is $20,000. The mean is $114,355, pulled upward by a small number of exceptionally high-impact findings, including a $10 million payout for one of the most significant vulnerability discoveries in the history of DeFi.
Now consider the alternative. Our hack impact research found that the median onchain hack in 2024-2025 resulted in $2.2 million in direct theft, and the average was $24.5 million. But direct theft is only the beginning. The median hacked token lost 61% of its value within six months, up from 53% in the 2021-2023 period. 84% of hacked tokens showed sustained price depression that they never recovered from within that window. And every hacked project lost at minimum 3 months of productive work to incident response, remediation, leadership turnover, and roadmap disruption.
The updated Amador’s Hack Impact Estimate puts the total cost plainly: if your protocol gets hacked today, expect to lose approximately $25 million in direct theft, watch your token shed 61% of its value, face an 84% chance of never recovering, and burn a quarter of the year on cleanup.
Set that against a $20,000 median bounty payment, and the math is not close.
The Uncomfortable Implication for Protocols Without Bounties
Here is what the data forces us to confront: there is no reason to believe that protocols without bug bounty programs have fewer critical vulnerabilities. They almost certainly have the same density of bugs, or higher, since the absence of a bounty program often correlates with less mature security practices overall. Bug bounty program or not, they will have critical vulnerabilities in their live mainnet code.
The difference is simple. With a bug bounty program, a researcher who finds a critical vulnerability has a clear, incentivized path to report it responsibly and get paid. Without one, that same researcher has no obligation and no reward. The vulnerability still exists. It just stays in the shadows until someone with less benign intentions finds it, or until it shows up onchain as an exploit.
And when it does show up as an exploit, the damage compounds in ways that go far beyond the initial theft. Our hack impact research documented how the growing interconnection of DeFi protocols has expanded the blast radius of individual exploits. Cross-chain bridges, liquid staking tokens, restaking derivatives, and composable lending markets have created dependency chains where a single compromise can cascade through the entire stack. The collapse of Elixir’s deUSD stablecoin, triggered by a $93 million loss at a single external counterparty, demonstrated how one failure can propagate through collateral dependencies to destroy a stablecoin, disrupt multiple lending markets, and wipe out over 97% of a token’s value.
87% of programs running for three or more years have had multiple confirmed criticals. The vulnerabilities are there. The only question is whether you’ve built a system to surface them before an attacker does.
The Industry Is Maturing, But the Threat Has Not Receded
Our hack impact research found one silver lining: the median theft per hack has declined from $4.5 million in 2021-2023 to $2.2 million in 2024-2025, which may partly reflect the maturation of smart contract security practices, including the growth of bug bounty programs. But this improvement is uneven and fragile. The largest exploits have grown even larger. The five biggest hacks in 2024-2025 accounted for 62% of all funds stolen. The market’s punishment for security failures has grown harsher, not more lenient. And the overall number of hacks remains stubbornly high, hovering around 95 per year.
The industry has not solved the security problem (yet). The protocols best positioned to survive are the ones that treat security not as a one-time audit but as a continuous, incentivized process.
What This Means
The takeaway from five years of vulnerability data and five years of hack impact data is the same story told from two directions.
Critical vulnerabilities are not rare. One in five confirmed bug reports across all Immunefi programs is rated critical.
Time reveals truth. The longer a program runs, the closer the critical discovery rate converges toward certainty. 93.9% of long-running bug bounty programs have surfaced a critical bug. Programs that haven’t received a critical vulnerability disclosure yet just haven’t been live long enough.
The cost of not looking is catastrophic. A $25 million average hack, a 61% token price decline, 84% chance of no recovery, and 3 months of lost progress. That is the price of finding out the hard way.
The math is simple. A $20,000 bounty that prevents a $25 million hack is the highest-ROI security investment a protocol can make.
Every serious protocol will face a critical vulnerability. The ones running bug bounty programs will find out from a whitehat researcher, on their own terms, with time to fix the issue before anyone is harmed. The ones without will find out another way.
This research is based on confirmed and paid vulnerability data from Immunefi, covering January 2021 through February 2026. Only traditional bug bounty programs were included; audit competitions and time-limited events were excluded from the analysis. Hack impact data is drawn from Immunefi’s The Real Cost of an Onchain Hack: 2024-2025 Update, covering 425 publicly known hacks across 2021-2025.