The Security Stack That Will Win Crypto Mass-Adoption
2025 was the worst year on record for crypto, with $3.4 billion stolen. And yet, smart contract hacks dropped to just 0.66% of total losses, a new low. Both of these things are true at the same time, and the gap between them tells us everything about where onchain code security is headed.
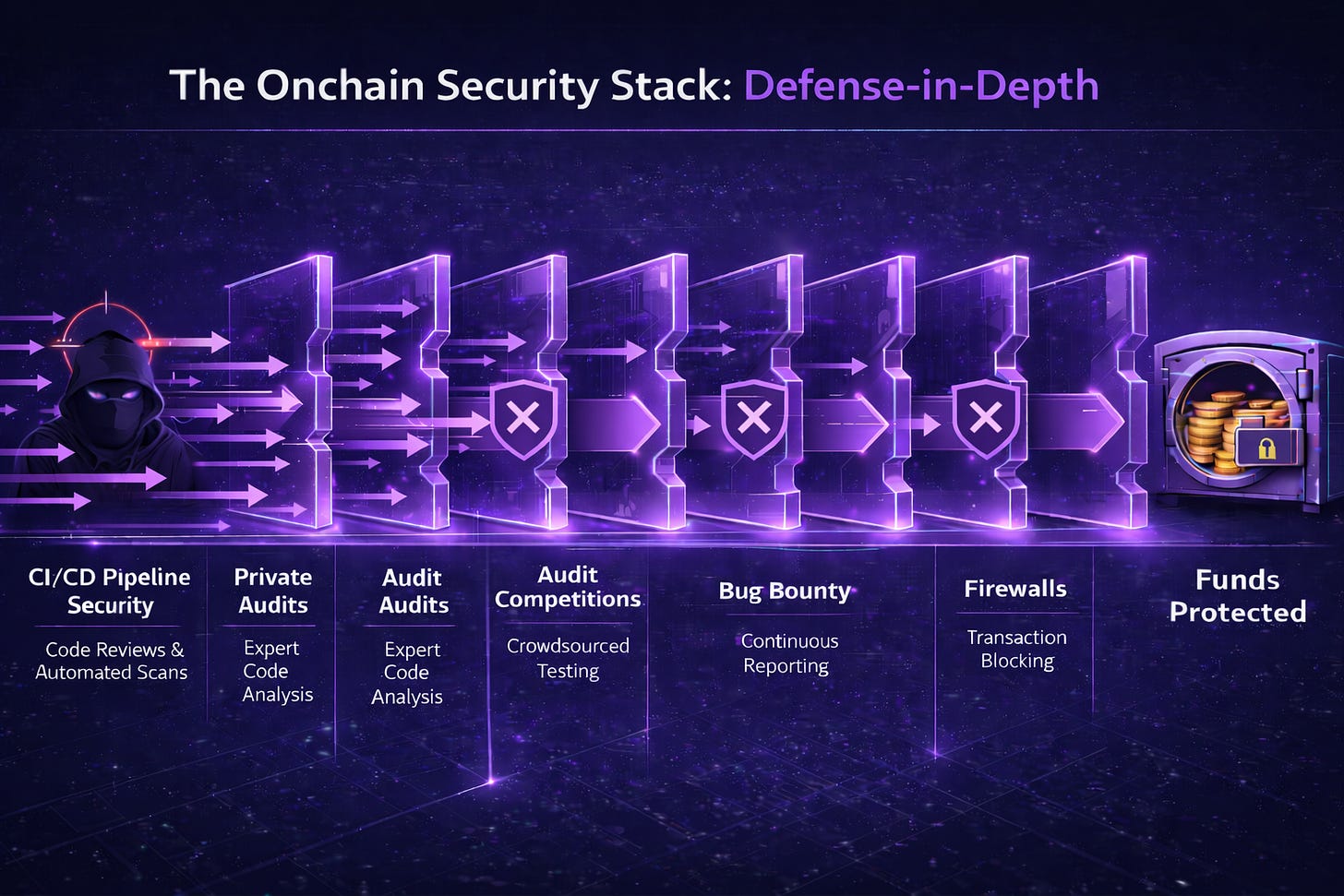
In short, the protocols that didn’t get hacked run what’s called “defense-in-depth,” and you should too.
The Swiss Cheese Model, Applied to Crypto
The defense-in-depth concept, also known as the Swiss cheese model, comes from risk engineering. Every security measure is a slice of Swiss cheese: each one has holes, no single layer is perfect. But stack enough slices together and the holes stop lining up. An attacker has to pass through every layer simultaneously to reach your funds, and the probability of that trends toward zero (though it will never reach it) with each layer you add.
This is not theoretical. I’ve seen the security setups of hundreds of protocols. The ones running a full defense-in-depth stack simply are the ones that are surviving, and that’s borne out in real smart contract impact rates which are (counterintuitively?) their best yet in 2025 at just 0.66% of TVL. The strategy is working.
The only barrier is adoption.
The New Onchain Security Stack, Layer by Layer
Here’s what a complete onchain code security stack looks like, ordered by when your code encounters each layer. In my view, every serious protocol should be running all of these within two years.
1. CI/CD Pipeline Security
Every pull request, every commit to a major branch, gets reviewed for vulnerabilities before it touches production. Automated vulnerability detection plus peer review on every code change. At Immunefi, we run this as PR reviews integrated into your GitHub workflow, with a combination of elite whitehats and AI vulnerability scanners.
Most vulnerabilities should die here, quietly, before anyone outside your team sees them. The cheapest place to mitigate an exploit is always the development pipeline.
2. Private Audits
A thorough point-in-time code audit from qualified security researchers who understand your system’s architecture and logic. You need this for major releases, protocol upgrades, and any significant change to how funds flow. The findings stay between you and your auditors until you’ve fixed them.
3. Audit Competitions or a Private Bug Bounty
Different from a private audit, and deliberately so. A competition opens your code to a broader pool of researchers competing against each other under a time constraint, surfacing a different class of bugs because you’re getting dozens or hundreds of independent perspectives instead of one team’s methodology. The competitive structure attracts top talent who might not be available for traditional engagements.
You could also structure it as a private bug bounty, wherein you invite top security researchers to break your code. It gets the same result if you structure the program right.
Run these before major launches. They complement private audits but they don’t replace them.
4. Public Bug Bounty Programs
Your permanent, always-on security layer. Every security researcher in the world has a financial incentive to find and responsibly disclose vulnerabilities in your live code, 24/7/365. This catches what audits missed, what changed since your last review, and what emerges from novel attack vectors nobody anticipated.
At Immunefi, ~92% of all critical crypto vulnerability disclosures flow through our platform. If you’re not running a bug bounty, you’re relying on attackers to find your bugs before whitehats do. That’s a bet you’ll lose eventually.
5. Safe Harbor
A legal framework that protects whitehat researchers who rescue funds during an active blackhat exploit. Without it, a researcher who spots an ongoing attack and moves funds to safety could face legal liability for touching those assets. Safe Harbor removes that barrier.
It costs you nothing to implement, and gives you another emergency response tool. It’s saved millions of dollars already. There’s no reason not to adopt.
6. Monitoring
Real-time observation of onchain and offchain activity around your protocol. Social monitoring catches coordinated attack chatter, and transaction monitoring catches anomalous fund movements.
This is your early warning system. It doesn’t prevent an attack by itself, but it could buy you the minutes that make the difference between a contained incident and a catastrophic loss.
7. Firewalls
Smart contract firewalls that pause or block suspicious transactions before they execute. If an attacker somehow passes through every previous layer, the firewall catches the anomalous transaction pattern and stops it. The final slice of cheese before the funds.
How to Sequence It
Building a full security stack takes time. You shouldn’t expect to have all layers running in place on day one. But there is an order of operations, and getting it wrong has cost billions to others.
First: Audits. Before anything else. Your auditors are not only reviewing code, but also educating you on how your security stack should work and helping you think through protocol architecture. This is where you learn what you’re protecting and how it can break. Start here.
Second: Audit competitions or a private bug bounty. Broader coverage, more eyes, different methodologies. This is your stress test before going live.
Third: Public bug bounty program. Your permanent layer goes up before or at launch. From this point forward, every researcher in the world can earn money by finding your vulnerabilities before attackers do.
Fourth: CI/CD pipeline security. Get your automated vulnerability detection and PR reviews into your development workflow so that every future code change is screened before it ships. If you can get this setup pre-launch, even better.
These four should be in place by launch day, or as close to it as you can manage. Safe Harbor, monitoring, and firewalls can follow, but don’t let “later” turn into “never.” Every week without a layer is a week where that slice of cheese is missing entirely.
Why This Matters Now
Security is the last great unsolved problem for crypto. When we solve it, tokenization eats the world, trillions move through crypto infrastructure, and every company becomes a web3 company. That’s the trajectory of the next five years, and the protocols that survive it will be the ones that made security a system rather than a specific event in time where they got an audit and stopped measures there.
No single product on this list is sufficient. An audit without a bug bounty leaves you exposed the moment your code changes. A bug bounty without monitoring means you might not notice an attack in progress. A firewall without underlying code review is a bandage on a wound you haven’t examined.
The whole point of defense-in-depth is that no individual layer needs to be perfect. Each one stops some attacks, and together, they stop nearly all of them. 2025 demonstrated that conclusively.
And the sooner we get these layers stood up across every major protocol in the space, the sooner we’ll unleash crypto to achieve its fullest and greatest potential.